White House: Top-level commitment led to USDA choice for modernization center of excellence
As the White House went about selecting its first partner to operate an IT modernization center of excellence, the U.S. Department of Agriculture was an apparent fit based on its buy-in from top leadership, according to Jack Wilmer.
The senior adviser at the White House Office of Science & Technology Policy said during a televised Government Matters interview Dec. 17 that “frankly, a lot of it comes down to top-level commitment” in the decision to tap the USDA for the first center of excellence.
“The Secretary of Agriculture [Sonny Perdue] was extremely supportive of modernizing agriculture.” Wilmer said. “I think that was one of his major objectives, and I think he understands the importance of IT in all of this.”
The Trump administration announced the plan last week to form its first center of excellence at USDA as part of a strategy incorporating industry stakeholders in collaboration with agency officials to develop an incubator-style program for future technology projects.
“We wanted to make sure that the first one that we roll out is going to be a success,” Wilmer said on the show. “So as we have the centers of excellence work with the departments, we want to make sure that first one is good and we can follow up rapidly with other ones, so Agriculture seemed like a perfect example.”
The centers of excellence model revolves around a central hub that develops research and best practices for innovation to develop solutions and jumpstart initiatives across a large sector — in this case, the White House is combining agency technology leaders with select contractors to drive modernization efforts.
Officials at the White House’s Office of American Innovation alluded to their plans for the centers of excellence model this past summer, followed by a request for information to industry in October outlining designs for four centers, each with a key technology initiative.
Wilmer also stressed the importance of total buy-in from agency leadership, including robust authority for CIOs as a key component of the center’s strategy and an integral factor in assigning future centers.
“I think that’s something that we are going to look at for the entire federal government as they modernize,” he said. “It’s really in conjunction with the IT shop because obviously, the CIO is going to play a critical role — and probably the most important role — but making sure they have very explicit support from their leadership is, I think is, a critical piece in modernizing.”
Tied closely to this plan is the recent enactment of the Modernizing Government Technology Act, which allows agencies to re-program unused funding to apply toward modernization efforts. The law provides $500 million to a central fund that agencies can draw from for IT projects.
Wilmer said that while funding will be in place to tackle some of the most pressing projects, the modernization ball is largely in the agencies’ court.
“The expectation is that the bulk of the funding is going to come from within agencies,” he said. “One of our big points of emphasis was trying to make sure that agencies were spending the dollars and people on things that are most important, and so I think that’s going to be one of the lenses we look through as we look to allocate the dollars: where are we going to get the best return on investment for those funds.”
White House takes We the People petition site down for maintenance
The White House took Petitions.WhiteHouse.gov — the website that hosts the We the People government suggestion box launched by then-President Obama in 2011 — offline for maintenance Tuesday.
According to an Associated Press story, the site was taken down at midnight. Visited on Tuesday morning, the web address hosted a simple announcement promising that the site will be back in “late January.”
“All existing petitions and associated signatures have been preserved and will be available when the site is relaunched,” the note states. “Following the site’s relaunch, petitions that have reached the required number of signatures will begin receiving responses.”
This is noteworthy because the Trump administration has been silent on whether or not it intends to keep up the tradition of responding to petitions that receive over 100,000 signatures. A visit to the Internet Archive confirms that 17 petitions exceeded this threshold, including one that calls for the release of Donald Trump’s tax returns (it was posted Jan. 20, 2017 and has over 1 million signatures). As The Verge noted in a story in March, the petition platform may have survived the initial Trump White House website reorganization, but it didn’t seem to be getting much attention.
Now that’s changed.
In an email to FedScoop, a White House official reiterated the promise that the website will be back in January and said that the maintenance work will “save taxpayers more than $1.3 million a year.” This doesn’t mean the White House is currently unreachable, the official said — “As always, Americans will be able to contact the White House any time by visiting whitehouse.gov/contact.” The official did not respond to a request for more specifics on the revamp or offer details on how the $1.3 million in cost savings will be realized.
The White House seems to be in end-of-year house cleaning mode — just this past Friday, the administration also unveiled its new WhiteHouse.gov site.
Tough road ahead in Senate for bill to create new DHS cyber agency
Despite passing the House and bipartisan support, the bill to create a new cybersecurity agency inside the Department of Homeland Security faces a tough climb in the Senate, observers and staffers say.
The Cybersecurity and Infrastructure Security Agency Act of 2017 passed by voice vote Monday — moving the bill to the upper chamber. In brief floor remarks, Rep. John Ratcliffe, R-Texas, called the bill a “compromise” that fellow Texas Republican House Homeland Security Committee Chairman Michael McCaul had worked on with “dogged determination.”
In a statement, newly sworn-in DHS Secretary Kirstjen Nielsen also praised McCaul’s “tireless work” on the proposal. It’s his second attempt — with bipartisan support from Rep. Bennie Thompson, D-Miss. — to create an operational cybersecurity agency within DHS. The first bill never made it to the House floor last Congress because of turf fights: Nine other House committees have jurisdiction over some element of DHS.
The latest attempt passed only because the three other committees with authority over cyber issues — Energy and Commerce, Transportation and Infrastructure and Oversight and Government Reform — relinquished their jurisdictional claims and allowed it to proceed.
The other committees did so, said staffers, in part because the bill was carefully written to limit its scope — specifically declaring that it’s not conferring any new authorities on DHS.
Instead, the bill simply renames the department’s National Protection and Programs Directorate, responsible for both the cyber and physical security of the nation’s vital industries. If the bill becomes law, NPPD will become the Cybersecurity and Infrastructure Security Agency and its current undersecretary will become a director.
“The bill [that failed] last year was much more ambitious,” said one Homeland Security committee staffer who asked not to be identified. “This year, to get it across the finish line, we crafted it much more narrowly … In my view, that shows the jurisdictional challenges we face.”
Red more about the bill’s passage and its tough road ahead on CyberScoop.
Don’t bring a sandwich slicer in your carry-on, and other tips from TSA’s first Facebook Live
“Blogger Bob” will be the first to admit that he has a quirky sense of humor, which is why, when asked about his favorite Transportation Security Administration Instagram post, he skips over the obviously exciting guns and knives and goes straight for the sandwich slicer.
Bob Burns, the brains behind TSA’s popular presence on the photo-based social media app (TSA has more than 800,000 followers), sat down for the agency’s first Facebook Live video stream Monday. He talked about how the account was started and his growth philosophy, and listeners were encouraged to ask him questions.
The Instagram grew out of a recurring theme on TSA’s blog, Burns said. In 2008 the agency started a blog, and in 2011 Burns started sharing some of the “crazy things” that TSA agents encounter out in the field. As a personal user of Instagram, Burns saw the potential, started posting pictures and “it just kinda blew up.”
He trolls through the “incident reports” that TSA agents have to submit after confiscating an item and picks the best of the best, he said. Everything posted to the account, he assured his Facebook Live viewers, is real and was really confiscated. Burns also has a knack for pairing the photos with captions full of puns, hashtags and his dry, quirky humor. This shock value, he believes, is a big part of the success of the account.
“People don’t come to a government social media account and expect to see humor,” he said.
Whatever the appeal, blow up the account certainly did. It has been featured in the Washington Post, Wired, Bon Appetit and more. It even beat out Beyonce (barely) in Rolling Stone’s 2016 top 100 Instagram accounts list.
The point was never just to win awards though, Burns said. Nor is it purely to entertain — the mission of the account is to educate travelers as to what they can and cannot bring on a plane as well as prepare them for a journey with some straight-from-the-source travel tips. The puns, the hashtags and the humor, Burns said, are attractive means to this end.
The best part of running this successful account, Burns said, is “the attention it’s brought to our workforce. That, you know, we’re not just finding small pocketknives — we’re actually finding dangerous things that people are trying to bring on planes.”
Burns knows the work firsthand — he started at TSA in 2002 as a screener before eventually moving into his social media role, he told viewers. So bringing attention to what work is like on the front lines is valuable.
“And in addition to our message, a lot of people are saying that our account brightens their day, you know, with the puns,” he added. “I’m glad to be able to help out with that.”
The Civic Digital Fellowship is coming back much bigger than before
When Coding it Forward opened applications for its Civic Digital Fellowship on Dec. 9, it was immediately clear the team has been hard at work since they were last in D.C. The program that brought 14 college-age tech fellows to the U.S. Census Bureau in the summer of 2017 is set to be much bigger this coming summer.
In 2018, in addition to the program’s existing relationship with the Census Bureau, fellows will join the State Department, the Department of Health and Human Services and two civic tech partners — the OpenGov Foundation and Represently. And in contrast to the 14 fellows who joined last summer, the 2018 cohort will expand to between 30 and 50, Coding it Forward cofounder Chris Kuang told FedScoop.
Students who apply for the program will flag their interest in a specific agency or civic tech organization, and that application will be passed along for review and a possible interview. Agencies will make their own hiring decisions where the skills of the applicant match the needs of the agency.
In addition to expanding its scope, the Civic Digital Fellowship is refining its pitch. When talking to would-be student participants, it’s all about creating a sense of the scale of impact that is possible from a role within the federal government.
“We’re really trying to make working in D.C. and working in civic tech cool for students,” Kuang said.
But there’s another thing the fellowship offers students, Kuang suggested — a blueprint for how to get interesting government tech jobs. The diversity of backgrounds that characterizes organizations like 18F and U.S. Digital Service employees can be confusing to an undergrad, he said. With the Civic Digital Fellowship, Kuang and his team are creating a pathway to better understanding them.
And what’s the pitch for agencies? Pipeline, pipeline, pipeline.
“That’s really what we’re passionate about, building that talent pipeline,” Kuang said. Coding it Forward promises to deliver precisely the kind of young tech talent the government wishes to attract (but often misses out on) — the first group of fellows came from Harvard and Cornell and MIT and more.
HHS CTO Bruce Greenstein, for one, was easily sold. “I don’t know how they ended up in my office,” he admitted in a recent conversation, “but I was blown away by the sophistication.” It was clear to him that the program was “so well thought-through” that HHS’ participation seemed a great opportunity. His job now is to sell the various HHS agencies on the idea of taking on some fellows (and setting aside the budget to pay them) — he hopes to bring in between eight and 12 total. Most of these, he said, will be data and computer science students.
It helps that Coding it Forward has immersed itself in a community of high-level government tech individuals — former Deputy U.S. CTO Nick Sinai is an advisory board member, as is Census Chief Marketing Officer Jeff Meisel and OpenGov Foundation cofounder Seamus Kraft.
Is there concern that the growth in numbers of fellows and agency partners is too much too fast? Kuang told FedScoop he’s not concerned — this time last year, the fellowship didn’t even exist and yet the team somehow managed to bring 14 students to the Census Bureau to work for 10 weeks on meaningful projects. So it’s safe to say there’s no lack of confidence here — 2017 was just the “beta test,” Kuang said.
“We’re extremely excited to be able to continue our journey,” Kuang said. “We’re really excited to bring more students to D.C. this summer and introduce them to the civic tech ecosystem.”
Hackers find Air Force vulnerability for biggest government bug bounty reward yet
A pair of white-hat hackers managed to find a critical vulnerability in an Air Force public website that let them access the Defense Department’s unclassified internal network.
Fortunately for the Air Force, it came as part of its Hack the Air Force 2.0 bug bounty, which it kicked off during the h1-212 hacking event in New York. The service invited non-Air Force hackers to seek out vulnerabilities in 300 of its public websites. The Dec. 9 event brought together security teams and ethical hackers “to discover as many vulnerabilities as possible,” according to HackerOne, the organization the Air Force contracted to host the bounty.
The service paid the security professionals, Brett Buerhaus and Mathias Karlsson, $10,650 for discovering the flaw. It’s the largest payout yet in a government bug bounty, though the top prize, according to the Air Force, could’ve been as much as $50,000.
“I didn’t expect how willing they were to work with us to figure out the issue and see how impactful it was,” Buerhaus told HackerOne. “There’s such a perception of the government being closed off and ready to sweep issues under the rug. It was great seeing how excited they were to work with us. This honestly changes everything, and it’s clear they care about working with us to protect their interests.”
At the end of the nine-hour day day, the Air Force paid out $26,883 in bounties and triaged each of the 55 reported vulnerabilities.
HackerOne has hosted other bug bounties for the Defense Department, most notably Hack the Pentagon, which was the first such bounty operated for a federal agency. According to HackerOne, “DoD has resolved over 3,000 vulnerabilities in public facing systems with bug bounty challenges and the ongoing [vulnerability disclosure program], and hackers have earned over $300,000 in bounties for their contributions — exceeding expectations and saving the DoD millions of dollars.”
To the delight of Air Force officials, it took participants less than 30 seconds to find the first vulnerabilities.
“Hack the Air Force allowed us to look outward and leverage the range of talent in our country and partner nations to secure our defenses,” Peter Kim, Air Force chief information security officer, said in a release. “We’re greatly expanding on the tremendous success of the first challenge by targeting approximately 300 public facing Air Force websites. The cost-benefit of this partnership in invaluable.”
Hack the Air Force 2.0 isn’t over, though. The service will continue accepting vulnerability reports until Jan. 1, 2018, from citizens in The Five Eyes countries — Australia, Canada, New Zealand, United Kingdom and United States — as well as those from NATO countries and Sweden. The inclusion of so many countries “makes the Hack the Air Force 2.0 challenge the most open government bug bounty program to-date,” HackerOne said.
GSA move to e-commerce marketplaces could open doors for acquisition reform
The General Services Administration’s move to make it easier to purchase supplies and products from online retailers like Amazon could also allow for a deeper examination of how the government handles acquisition in the 21st century, a former Department of Defense acquisition official said.
GSA is moving to incorporate industry input into a strategy to set up e-commerce portals for federal agencies. The agency is taking public comment on an implementation plan that has a March deadline under a provision in the fiscal 2018 National Defense Authorization Act.
“I actually think this is a good idea,” said Stan Soloway, president and CEO of contractor consultant firm Celero Strategies and a former deputy undersecretary of Defense for acquisition reform. “Not because it’s going to have an enormous, seminal impact in and of itself. It will probably be a relatively limited application to start. But it opens up a much broader conversation. And it’s time to have that conversation about what is the future of federal procurement, particularly when we are dealing with commodity items that can now be acquired in streamlined, often machine-driven and machine-run ways?”
The plan was included in the NDAA by House Armed Services Chairman Mac Thornberry, R-Texas. It calls for an initial implementation 90 days after the enactment of the bill, which would be a March 12, 2018, deadline.
GSA, which is developing the e-commerce portal program with the Office of Management and Budget, said in a Dec. 15 Federal Register notice that it would begin a series of town hall-style sessions to garner public comment, with the first scheduled for Jan. 9 at its headquarters.
But even in the early days of this process, Soloway said there is a litany of things that GSA will have to navigate to build a structure allowing for e-commerce procurement.
“To actually develop an implementation plan, even for this initial launch, really requires some deep-diving into processes that I’m not sure that any of us understand yet,” he said. “How much can any of us say with great, detailed knowledge about how a Staples or a Walmart or an Amazon, how the internals of it work?
“I think the real challenge for GSA, at least initially, is really mapping out all of those components and really understanding where and how they align or do not with both federal processes and systems and also the requirements of the legislation.”
Understanding the different internal processes of multiple e-commerce retailers will provide GSA the opportunity to sift through a wealth of information before it designs a system for federal use.
The benefit is that the system GSA design could help inform the future development of other acquisition programs to help reform the government’s procurement systems, Soloway said.
“It could take some workload pressure off an overworked acquisition community and really focus their time and energies on the stuff that is complicated and really requires their skillset as opposed to more routine stuff they end up spending time on that is really an unnecessary use of their skills,” Soloway said.
According to the NDAA, after the agency submits the implementation plan to Congress, it will have a year to incorporate changes and technical considerations. Following that, the agency has an additional year to craft guidance.
House Oversight Committee wants GAO to look into five areas of IT modernization
After helping to push a key piece of IT legislation – the Modernizing Government Technology Act — to enactment this year, the House Committee on Oversight and Government Reform is asking for answers about the state of federal IT talent, the outcomes of recent modernization projects and more.
The committee sent a letter to the Government Accountability Office last week expressing its continued interest in the topic of IT modernization and specifically asking GAO to look into five additional areas.
To build on the reports that GAO already prepares on IT, the committee asked the watchdog agency to take a look at:
- Best practices from agencies that have been successful in implementing the Federal Information Technology Acquisition Reform Act (FITARA).
- How agencies are doing in their Portfolio Review requirements pursuant to FITARA.
- The acquisition status of the top 15-25 IT mission critical IT systems “for the nation.”
- The status of the top 10 legacy IT modernization projects and the top 10 modernization successes of the past five years.
- The current state of and challenges facing IT human capital in the government.
“The Committee has spent considerable time overseeing the federal government’s IT spending and implementation of FITARA,” the letter states, and now that the MGT Act is on the books, the panel is preparing to “conduct oversight to ensure effective implementation” of that law as well.
The Presidential Innovation Fellowship program cruises along after surviving its first transition
In political science, the first peaceful transition of power is a defining moment for a new democracy — it lends legitimacy to what was previously just the policy of a ruling party. The moment a new leader respects the status quo, democracy is solidified.
The same could be said for government programs transitioning to a new administration.
When President Barack Obama left office, there was some handwringing over what might befall his signature innovation initiatives in tech and science. And while the jury is still out on some (What, for example, is happening at the Office of Science and Technology Policy?), others are cruising right along.
Take, for example, the Presidential Innovation Fellows program. Started by the Obama administration in 2012, the first cohort under President Donald Trump began its tenure nearly two months ago. After the last-minute passage of the TALENT Act codified the program, things are advancing very much as expected, acting Executive Director Ben Willman told FedScoop.
Willman is new to his role as director but an old hand at the program. He was a fellow — the group is often called PIFs — back in 2013 as part of the second round of the program.
Members of that class had staying power — people like Chris Cairns and Aaron Snow went on to form 18F, the government’s digital agency within the General Services Administration. Willman joined 18F too for about a year, before returning to the PIF program as director of strategy.
Since August he’s been serving as acting director and working to rebuild the program’s administrative team. Everyone involved in the PIF program, the fellows themselves and the administrative staff, are hired for short-term contracts with the possibility of extension. This hiring authority rarely extends for more than four years, Willman said.
This meant that when Willman stepped into the director role, he found the rest of the office unstaffed — he brought on Joshua Di Frances as director of operations and Saran Kaba as an operations specialist. The team is “lean” (Di Frances’ word) by design — there’s just one more role (director of communications and marketing) to fill.
But that’s not all Willman has been doing. He also presided over the kickoff of a new cohort of PIFs. The post-inauguration hiring freeze meant the class got off to a late start, but beyond that, Willman said, it’s been business as usual.
“It shows that the work that the fellows are doing is bipartisan, good-for-government work that everyone can get behind,” Willman said in a recent conversation. “It’s exciting that fellows can continue to do this.”
Has the passage of the TALENT Act made a difference in how agencies view the program? Willman said it hasn’t made an operational impact “yet.”
“I would say that we are still engaging agencies and having the same conversations that we were before,” Willman said. “It is nice that we get to reference [the TALENT Act]. But agencies come to us with their problems and challenges, which they did before the TALENT Act and they still do now.”
The program works the same way it always has — PIF leadership meets with agencies to discuss the work a fellow might be able to do. What makes a good PIF problem? It’s all about the guidelines, Di Frances said — or rather the lack thereof.
If an agency knows exactly what problem it wan ts to solve and what it wants to build to solve it, a PIF won’t add much value. The perfect PIF problem, Di Frances told FedScoop, is a bit more “nebulous” — an important problem with potential for impact, but one that requires creative thinking.
“We’re looking for people who are used to starting things in ambivalent or difficult situations,” Willman said. In other words, people who thrive “where the work is not all laid out for you.”
The elephant in the room, of course, is whether the Trump administration is reducing interest in the program. Is “Presidential Innovation Fellow” still a sought-after title? Willman suggested he thinks so, but can’t be sure.
“We had the same high interest across all the other rounds, the application pool was strong,” he said. But “because people self-select to apply, we don’t really know what an effect would have been had the election differed, because we don’t hear about that.”
FEMA looks to the cloud to scale services and deliver better customer experience
Federal agencies recognize the importance of improving the customer experience and how technology can help. In this abridged Q&A, Federal Emergency Management Agency CTO Ted Okada shares how FEMA is marrying customer feedback with data analytics and cloud-based services to improve the customer experience for victims of disaster and for first responders.
FedScoop: How important would you say technology is to FEMA’s mission — and to understanding and managing the customer experience?
Okada: In our mission statement, we are to support citizens and first responders, state and local government, but first and foremost, survivors of disasters. When I think customers, I think of those survivors who are in the disaster zone and how do I meet their needs best? We work as a team — the back office is the front office — from solution design or early problem identification or pain points, all the way through how that translates into a solution and long-term infrastructure.
FS: What steps has FEMA taken over the past year or two to improve the way it measures and uses customer experience feedback to judge how it’s doing and to enhance program performance?
Ultimately, we want happy survivors. We want to ensure that these survivors are not in harm’s way again … and that communities and states can understand their risk. Those things are the ultimate metrics — where we can reduce loss of life and the loss of property.
When I look at decisions, I use this meme: “How do you leverage the power of algorithms, the insight of the experts and the wisdom of the crowds?” We’re trying to get better standardized tools … and better analytics. [and focus on] what I call the aperture of data. The wider the aperture, the easier it is to generate better insight because the field of data is larger. We’re now sharing more machine-readable data than human-readable data.
As a government, it’s not just that we do analytics, but that we empower citizens and universities and the press to run analytics.
 That’s why we created “OpenFEMA.” We want to be increasingly transparent. We don’t have all the solutions. It’s our first responders and our states that really at the front line. We’re just in the back supporting them.
That’s why we created “OpenFEMA.” We want to be increasingly transparent. We don’t have all the solutions. It’s our first responders and our states that really at the front line. We’re just in the back supporting them.
The fascinating development with the modernization of IT systems within FEMA is that APIs are driving the aggregation of data across systems. As we modernize and standardize on consistent, repeatable, predictable software infrastructure which is open source, we’re
certainly going to be on solid technical ground.
FS: If you were a citizen, how might you describe how FEMA’s customer experience feels better tuned to their needs?
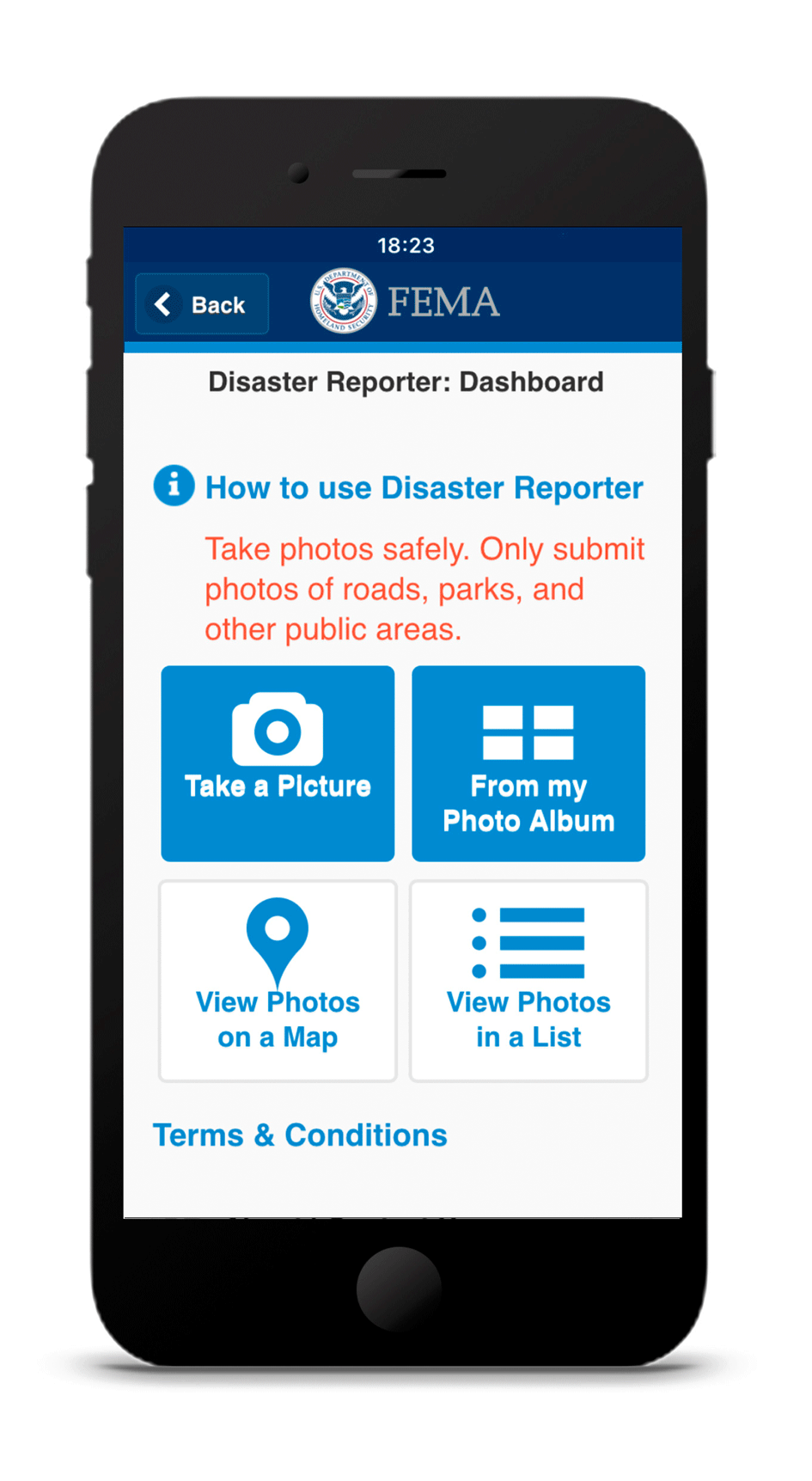
Okada: We have a feature called “Disaster Reporter” that allows for citizens to take photos of hazards, upload them and then they are shared by FEMA. We want everybody in the nation to use the FEMA app. The experience that really matters is that of the disaster survivors themselves. The former administrator used to say, “In a disaster, your world is as far as you can see, as far as you can hear, and as far as you can walk.” That is a different experience than most of us have every day. When I look at web design, mobile app design or any design, it’s not just an IT issue. What is the fundamental process? Is that process easier for the survivor? Is it easier for the local mayor or the local county or the state governor and their offices? That’s what’s driving us. Is it easier for them? They are ultimately my customers, the survivor and the first responder.
FS: What might have been easier for survivors to accomplish after this year’s Hurricanes Harvey, Irma and Maria compared to past disasters?
 The challenge about this year in particular is scalability. We’ve had to take our entire infrastructure and scale it to literally millions of people to register for assistance. We’ve sent billions of dollars in assistance very quickly. We’ve had to target populations to [provide] housing solutions very quickly … and repeat this process over four major catastrophic disasters. We are having to scale this beyond what we’ve ever scaled before. Now we’re going to have to sustain it for many, many years ahead. So, when we say we need processes that are measurable and manageable, it’s also about them being repeatable, sustainable, scalable.
The challenge about this year in particular is scalability. We’ve had to take our entire infrastructure and scale it to literally millions of people to register for assistance. We’ve sent billions of dollars in assistance very quickly. We’ve had to target populations to [provide] housing solutions very quickly … and repeat this process over four major catastrophic disasters. We are having to scale this beyond what we’ve ever scaled before. Now we’re going to have to sustain it for many, many years ahead. So, when we say we need processes that are measurable and manageable, it’s also about them being repeatable, sustainable, scalable.
FS: What’s changed to allow FEMA to scale at this level compared to a couple years ago?
Okada: We’re doing a lot in the cloud, of course, which allows us to scale. I’d say the hidden benefit is actually what we’ve done in raw engineering inside our IT shops… with internal databases. Scaling our internal financial
systems has been the biggest challenge. Cloud computing can be a catchall phrase, but really, it’s about how you get databases to perform faster and deliver that content faster via the web. We are in a situation where we now can begin to modernize a lot of those databases to perform much more effectively than in the past.
FS: Looking ahead, what other areas are you focusing on in the way of user experience and design?
Okada: Being immersive. There are a lot of ideas germinating in emergency management. How are
emergency management systems, crisis management systems viewed through the lens of the end user? How do we integrate it from the state level to the federal level? Is the right kind of data getting to the right people at the right time? Those classic questions about system design.
Also, cybersecurity. How do we authenticate users using single sign-on on devices so they don’t have to memorize passwords? We are getting them to that single sign-on future through two-factor authentication and FEMA’s really leading the way in that.
Read more about how Accenture is helping agencies deliver superior customer experiences.