Cybersecurity incidents down at federal agencies, no ‘major’ ones

Agencies saw a 12% decrease in cybersecurity incidents between fiscal 2017 and 2018, and none met the “major” incident threshold in fiscal 2018, according to an annual report to Congress.
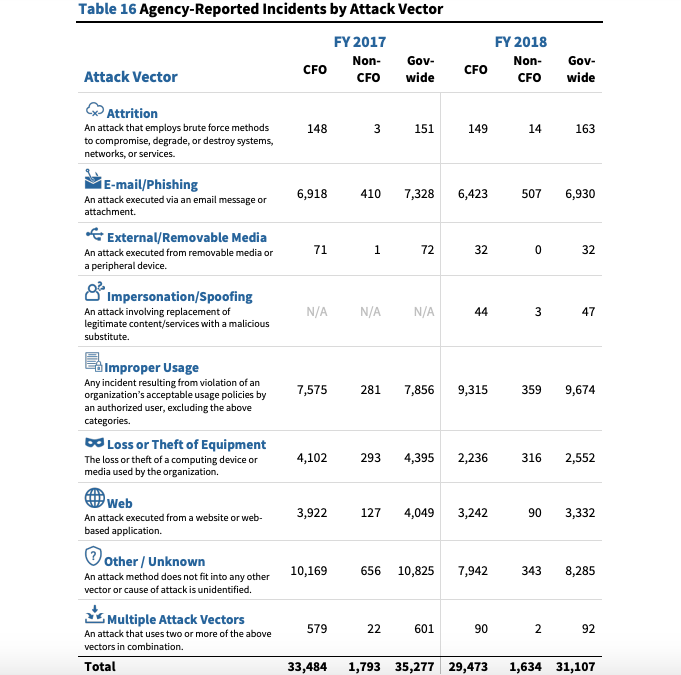
The Office of Management and Budget found agencies endured 31,107 incidents between Oct. 1, 2017, and Sept. 30, 2018 — down from the 35,277 reported the previous fiscal year — in the latest Federal Information Security Modernization Act report.
OMB defines a major cybersecurity incident as one likely to harm U.S. national security, foreign relations, economics or public safety. Included in the definition are breaches where personally identifiable information is compromised in a way that threatens such interests.
No major cyber incidents occurred in fiscal 2018, according to the report.
“While the trend is encouraging, drawing conclusions based on this data point, particularly as agencies have adjusted to several new sets of reporting guidelines over the last few years, would be concerning,” reads the report. “[E]mail-based threats remain prevalent, with email/phishing continuing to be a highly-targeted attack vector.”
The Department of Homeland Security, which monitors federal networks, reported 6,930 such incidents governmentwide in fiscal 2018. And 27% of all incidents lacked an identified attack vector — suggesting “government must take additional steps” to assist agencies in analyzing attacks, according to the report.
OMB found incidents resulting from violations of agency usage policies by authorized users remained the largest identified attack vector and external/removable media the smallest.
OMB also evaluated how 97 agencies were managing their cyber risk at the enterprise level using fiscal 2018 Chief Information Officer Metrics. The metrics’ “domains” correspond with those of the National Institute of Standards and Technology’s Cybersecurity Framework: identify, protect, detect, respond and recover.
An agency was deemed “high risk” if fundamental cybersecurity policies, processes and tools were either not in place or deployed sufficiently. “At risk” agencies implemented some essentials to mitigate risk but with significant gaps remaining. And an agency was said to be “managing risk” if federal requirements were met and actively managed.
Of the 23 civilian Chief Financial Officers Act agencies, 19 were found to be managing risk, and three — the Department of Energy, Department of Health and Human Services, and Environmental Protection Agency — were categorized as at risk. The Federal Emergency Management Agency was included under the Department of Homeland Security.
More broadly, 62 of the agencies evaluated were found to be managing risk, 32 at risk and three — the Morris K. Udall Foundation, Smithsonian Institution and Vietnam Education Foundation — high risk.