Online ‘honor roll’ — small boost in feds’ website security


The 2016 Honor Roll is the eighth the Online Trust Alliance has produced.
The 50 top federal government websites have improved very slightly overall this year on a scorecard of security, privacy and consumer protection measures, but more than half still got a failing grade, according to the Online Trust Alliance’s 2016 Honor Roll.
The top scorer in the federal sector was HealthCare.gov, followed by the White House, the Federal Trade Commission, the Social Security Administration and the U.S Postal Service.
Altogether, 23 of the 50 websites, or 46 percent, made the Honor Roll — meaning they employ a baseline set of security, privacy and consumer protection measures widely recognized as best practices. That compares to 44 percent of the top-500 internet retailers, and 55 percent of the top 100 federally insured banks. Last year, just 21, or 42 percent, of federal sites made the cut.
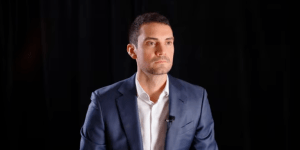
“There’s some positive movement, but there is no reason why all of these [federal] sites shouldn’t be on the Honor Roll,” OTA Executive Director Craig Spiezle told FedScoop. “The good news is, we tighten the standards and raise the bar every year, and despite that, we’re seeing better results.”
The Centers for Disease Control and Prevention, the Department of State, the General Services Administration and the Federal Deposit Insurance Corporation were all bumped from the roll this year, after having qualified for last year’s list. FDIC’s exclusion was especially notable because it led the entire federal sector last year.
“FDIC had one of the best scores” this year as well, Spiezle said, but it was knocked out of the running because of the multiple breaches it disclosed to Congress last month.
“A single breach will not disqualify you,” he said. “A determined adversary is almost always able to get through” even the best security. But he said the scoring system used for the Honor Roll punished multiple breaches heavily, on an exponentially rising scale after the first one.
“Anyone can get a breach,” he said. “But five? That suggests there may be some issue with operational discipline, with procedures not being followed or security issues remaining unaddressed.”
Spiezle said the scoring system OTA uses for the Honor Roll each year is based on the implementation of “widely accepted norms and standards, including those produced by [the National Institute for Standards and Technology] and [Office of Management and Budget].”
He said that OMB security directives, including those issued after the disclosure last year of the massive hack against the Office of Personnel Management, were one reason for the progress federal sites had made.
“It is all about walking the talk,” he said.
The principle reason so many federal sites failed, Spiezle said, was a lack of email authentication, which hobbled all but two of the 27 sites that failed.
“Some of these agencies might argue, ‘Well our site is not consumer-facing,’ but our attitude is, we don’t think anyone’s immune,” he said.
Email authentication is a major part of the consumer protection score that OTA awards each website, because it prevents the spoofing or impersonation of email addresses and is therefore an important weapon against phishing and spear-phishing — the two most common techniques used by cybercriminals to infiltrate a company or department network or to steal personal data from a user through trojan malware or keyloggers.
In spoofing, hackers make it look as though email comes from a legitimate company, like Chase.com or Apple.com, to fool recipients into clicking infected links or giving over personal data like passwords or account numbers.
Two measures — the Sender Policy Framework, or SPF, and the Domain Keys Identified Mail or DKIM — help a recipient’s email provider determine whether the sender is really authorized to send email from the domain in the address.

This OTA graphic outlines how email authentication provides the ability for ISPs and receiving networks to detect and block spoofed and forged email.
“They are complementary technologies,” said Spiezle of SPF and DKIM. “They address each others’ shortcomings.”
The third element is a protocol called Domain-based Message Authentication, Reporting and Conformance, or DMARC. DMARC basically tells email providers what to do with messages that can’t be authenticated through SPF or DKIM. Without DMARC, messages that fail authentication typically end up in spam folders, but with it, most will simply not be delivered at all.
The Honor Roll audits almost a thousand websites from a broad selection of sectors, including banks, internet retailers and consumer or social media sites like Twitter. “We use the same criteria for every sector,” Spiezle said. “It’s an apples to apples comparison.”
He said the objective of the exercise was not to “name and shame” — companies that fail are not named, although those that fall off the roll from one year to the next can be identified. “We want people to improve.”
“It’s all about evangelizing and promoting better security, driving best practices and measuring adoption,” he said.
Contact the reporter on this story via email Shaun.Waterman@FedScoop.com, or follow him on Twitter @WatermanReports. Subscribe to the Daily Scoop to get all the federal IT news you need in your inbox every morning at fdscp.com/sign-me-on.