DIU looks to automate cyberthreat detection for military IT networks
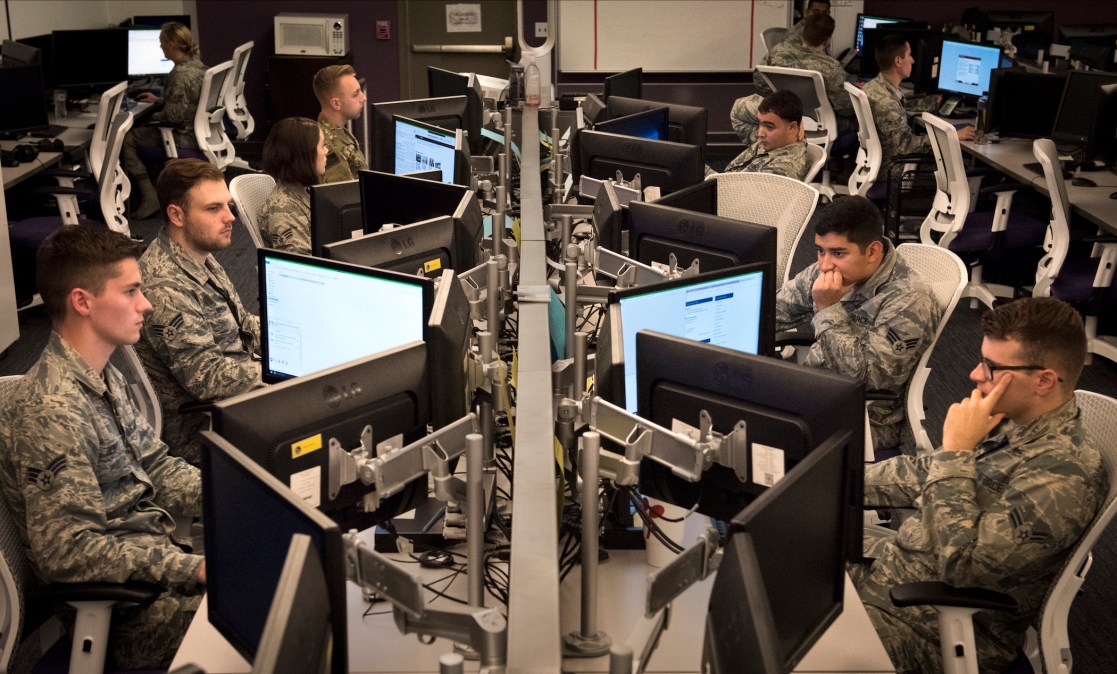
As the military services look for ways to address the dual challenge of workforce shortages and increasing cyberattacks, the Defense Innovation Unit issued an other transaction agreement (OTA) for a new automated cyber product.
The prototype will bring an “intelligent decision automation platform” to the Air Force Network (AFNET) built by Respond Software, a California-based software company that uses automation to detect attacks. The code behind the automation draws from a relatively old form of artificial intelligence called “expert systems” that, instead of creating large neural networks based on data, uses advanced probability-based mathematics that simulates decision-making.
While the prototype is starting with the AFNET, if it’s successful, DIU is looking to scale it across the military, Jeff Kleck, cyber portfolio director for DIU, told FedScoop. The prototyping of the platform is another attempt by the Air Force, replicated by other branches of the military, to automate cyberdefenses and ease the burden on cybersecurity professionals that come in limited supply.
“Today they really don’t have a chance; it is a tidal wave of alerts,” said Mike Armistead, Respond’s co-founder and CEO.
Previously, Air Force innovation officials have said they want to use artificial intelligence technology to support basic cybersecurity and reserve un-programable human ingenuity for offensive and bigger-picture work.
In developing the prototype product, Respond will use simulated network attack data while it works through the authority to operate (ATO) and Federal Risk and Authorization Management Program (FedRAMP) processes.
“During the lab trials/testing phase prior to obtaining ATO, these products are fed synthetic or anonymized data, and traffic emitting from connected modules are scrutinized for leakage and repudiation risks,” Kleck said. He later added that “as part of our prototyping process DIU runs products in a controlled environment before ATO.”
The tool aims to better triage and limit false positives in automated cyber threat detection and link together different sensors on the Air Force’s network, according to the company. Respond’s capabilities are modeled after human decision-making, like being able to “connect the dots” and seek out patterns.
“What we have done is put that into software, which has a very different scale to it,” said Armistead.






