14 new security ‘deficiencies’ found in IRS information systems

IRS information systems and data are at risk due to weaknesses in access controls and other security procedures, according to a new report.
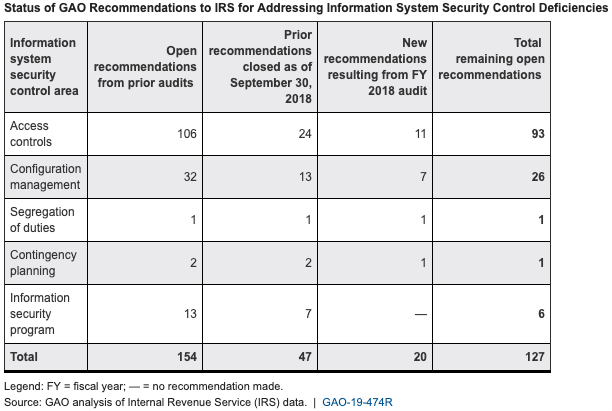
The Government Accountability Office audited IRS financial statements from fiscal 2017 and 2018 and found 14 new “deficiencies” in information system security controls — on top of unresolved problems from prior audits. If compromised, information systems can be used to commit fraud or identity theft, disrupt operations, and launch attacks on other computer networks.
Of the new issues, eight pertained to access controls, four to configuration management, one to dividing duties, and one to contingency planning.
GAO detailed each weakness and made 20 recommendations to the IRS, bringing the total number of unaddressed recommendations across audits to 127.
“Until these new and continuing control deficiencies are fully addressed, IRS financial reporting and taxpayer data will remain unnecessarily vulnerable to inappropriate and undetected use, modification, or disclosure,” reads the GAO’s public report.
Access controls — where the IRS had the most deficiencies — limit and detect unauthorized access to programs, data and facilities, and encrypt sensitive information. GAO found the IRS didn’t enforce use of the proper certificates to electronically sign tax documents, consistently enforce maximum password age limits for certain Oracle database accounts, or use multi-factor identification to access certain applications.
The IRS also failed to disable an app function allowing certain user accounts to download the entire database of information it contained, as well as prevent user accounts from having unnecessary access to tax processing system databases, according to the report.
With respect to cryptography, GAO found the IRS didn’t encrypt certain servers and email services like it was supposed to or enforce certain encrypted database connections.
On the configuration management front, the IRS didn’t implement mandatory access controls for an application, update unsupported database software or apply vendor-supplied patches in all cases, consistently update third-party software on workstations, or upgrade outdated and unsupported software network devices, according to the report.
In one flaw dividing duties, GAO found the IRS allowed a non-administrator account access to an administrator database.
The IRS also fell short in contingency planning by assigning only one person to administer its email service, according to the report.
IRS agreed with GAO’s recommendations with plans to conduct a root cause analysis of sustainable fixes. The fixes will be evaluated during GAO’s audit of the IRS’s 2019 financials.






