After news of SolarWinds breach, Capitol Hill turns attention to CISA
Cyber-savvy members of Congress were just beginning to respond, as of Tuesday morning, to news of breaches of at least three federal agencies’ networks by foreign hackers, but the early reaction from Capitol Hill focused on supporting the Cybersecurity and Infrastructure Security Agency to do more work to protect the government.
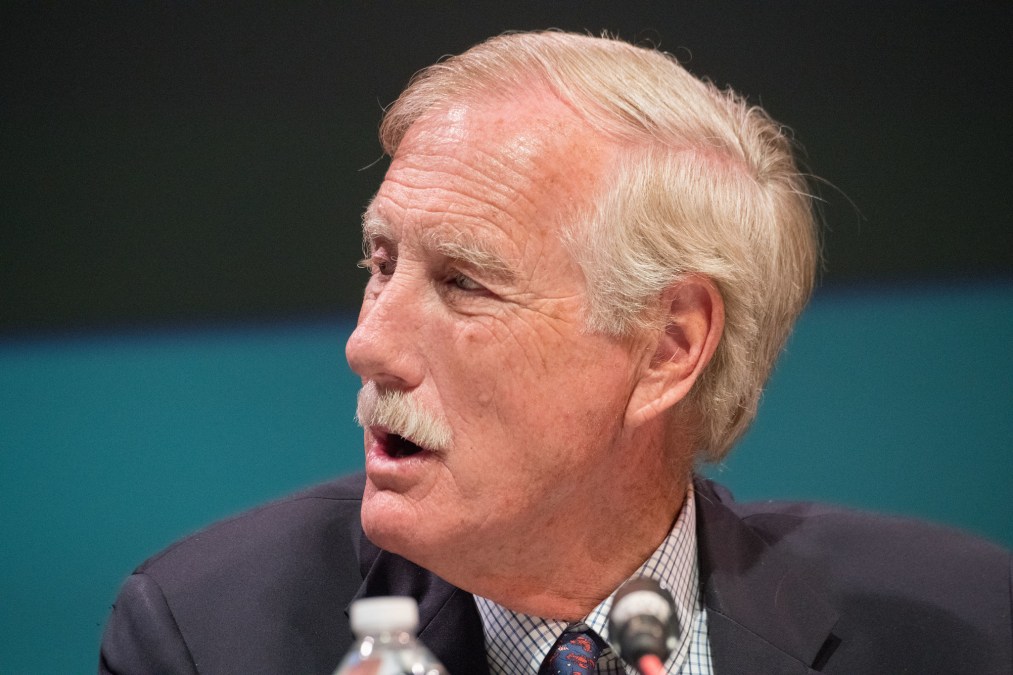
Sen. Angus King, D-Maine, offered one of the more nuanced early responses in advocating that CISA should get expanded authority to hunt for threats on the .gov network.
CISA gave agencies using SolarWinds products until noon Monday to review their networks and disconnect or power down the company’s vulnerable Orion software, but now its cyber protection teams must begin the daunting task of rooting out malware and restoring compromised security.
“This is going to continue,” King said in a statement. “[Vladimir] Putin can hire 8,000 hackers for the price of one jet fighter, and this is a way that he can attack this country and do relative damage at a very low cost.”
King co-chairs the Cyberspace Solarium Commission, which continues to craft a doctrine on cyberattacks and recommended this year’s National Defense Authorization Act (NDAA) enable CISA to find vulnerabilities faster.
Instead, cybersecurity firm FireEye accidentally discovered that foreign spies were using SolarWinds’ updating system to disperse malware — allowing them to hack the departments of Commerce, Homeland Security and Treasury — while investigating its own hack. And nine months too late at that.
King and other lawmakers were grappling with the fact that SolarWinds has been a trusted vendor supplying at least 32 agencies with network and infrastructure monitoring and management software since 2006. Orion is the framework that ties its tools together with tendrils reaching into the most sensitive parts of agencies’ networks.
“As we learned in the NotPetya attacks, software supply chain attacks of this nature can have devastating and wide-ranging effects — whether it’s via niche Ukrainian tax software or, as here, network management tools relied upon by some of the world’s largest companies,” said Sen. Mark Warner, D-Va, vice chairman of the Intelligence Committee, in a statement. “As we gather more information on the impact and goals of these malign efforts, we should make clear that there will be consequences for any broader impact on private networks, critical infrastructure or other sensitive sectors.”
Consequences have been few under the Trump administration, which has shown a reluctance to rebuff Russia — whose hacking group APT29, or Cozy Bear, staged the campaign on behalf of the SVR intelligence agency, The Washington Post first reported.
President Trump also fired CISA’s highly regarded director, Chris Krebs, when the agency debunked the president’s false claims of widespread voter fraud in his failed reelection bid.
“The recent data breach revelations are further proof of the Trump administration’s reckless posture toward cybersecurity,” said Rep. Robin Kelly, D-Ill., via email. “Firing Director Chris Krebs and not having a national cybersecurity coordinator serving on the [National Security Council] will likely harm coordination and slow down the interagency response.”
CISA held a briefing for congressional staffers Tuesday evening, revealing another agency confirmed it was affected by the SolarWinds incident after responding to the emergency directive. But it’s unclear if that referenced DHS or a fourth, as-yet-unidentified agency.
The Department of Commerce further briefed the Senate Commerce Committee on the cyberattack it suffered, including Sens. Roger Wicker, R-Miss., John Thune, R-S.D., and Jerry Moran, R-Kan.
“While many details are still unknown, the attack emphasizes the importance of strong cybersecurity protections and rapid incident responses across all federal agencies,” they said in a joint statement. “Cyberattacks by nation-states like Russia and China threaten our economy and national security. Our response should be swift and clear.”
Wicker’s bill the Harvesting American Cybersecurity Knowledge Through Education (HACKED) Act, which Thune co-sponsored, was included in the recently passed NDAA.
The legislation would enhance agencies’ cyber workforce by establishing cybersecurity awareness standards for them. But President Trump has threatened to veto the bill unless a provision that would rename bases currently named after Confederate leaders is dropped, a veto that Congress would certainly override.
Still such legislation doesn’t help with the task at hand: figuring out how many agencies were affected by the SolarWinds breaches, where malware moved within their IT infrastructures and what data was compromised.
“Once we understand the full scope of the damage, the administration must immediately work to eliminate the vulnerabilities that led to this attack and strengthen our cybersecurity systems to prevent future attacks,” said Sen. Maggie Hassan, D-N.H., in a statement. “The Senate Homeland Security Committee must make this a top priority.”






