- Sponsored
- Modernization
New-era authentication key widens trusted access to federal resources

The recent wave of highly public cyberattacks has cast a spotlight on last month’s White House executive order on cybersecurity, and the need for agencies to modernize their cybersecurity and authentication systems.
The executive order’s call for implementing zero-trust architecture, and new requirements to focus on more modern authentication strategies, signals an important turning point for government, say cybersecurity experts.

Read the full report.
“This executive order will affect many organizations, both in the public and private sector, that work with the government [including] financial services, healthcare, the public sector, critical infrastructures, high tech, and education,” commented David Treece, Director Solutions Architecture at Yubico in a new report on modernized multifactor authentication (MFA) strategies.
The new directives lay out the need for agencies to implement a more multifaceted and modernized approach to authentication that can support today’s widely distributed and dynamically configured networks, according to a new report, produced by FedScoop and underwritten by Yubico.
The limits of CAC/PIV cards
The report highlights the rapidly evolving nature of authentication tools and the need for agencies to expand upon traditional public key infrastructure (PKI) methods. While the government’s long-established PKI-based Common Access Card (CAC) and Personal Identity Verification (PIV) credentials remain foundational to controlling access to defense and civilian systems respectively, they still have their limits.
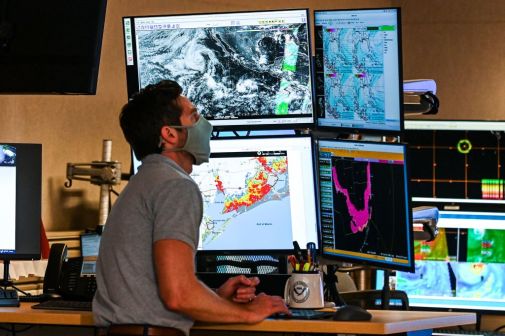
Those working in command centers requiring simultaneous access to multiple systems, for instance, can generally only use their CACs to access one system at a time. CAC and PIV cards also require specialized contact-based card readers — to prevent someone from eavesdropping on the traffic that goes between the card and the card reader — making them difficult to use with modern devices such as mobile smartphones and tablets.
Those and other limitations led a small group of engineers from Yubico in 2008 to develop the YubiKey, a hardware security key that utilizes DoD-approved PKI cryptography and Identify Federation Service (IFS) solutions to authenticate users as an alternative to CACs.
YubiKeys provide “a form factor that is as strong as the CAC or the PIV and can be used across multiple devices without a smart card reader,” explains Jeff Frederick in the report. Frederick is lead technical resource for the public sector team at Yubico. The YubiKey has since become a DOD-approved alternative authenticator.
Fast forward to the advent of cloud computing, the ubiquitous reliance on multiple mobile computing devices, and most recently, the massive redistribution of the government’s workforce during the pandemic, and the need for more modern and adaptable alternatives to multi-factor authentication has grown exponentially.
That led Yubico to work with various certificate authority (CA) vendors as well as with Google, Microsoft and other leading technology suppliers to advance the capabilities of remote authentication, says Frederick.
Most notably, Yubico became a founding member of the non-profit FIDO (Fast Identity Online) Alliance, formed to address the lack of interoperability among authentication devices. Yubico engineers have also teamed up with organizations to develop open, scalable and interoperable mechanisms which work effectively in the cloud and ultimately, are aimed at supplanting the reliance on passwords.
That has spawned a comprehensive line up of YubiKeys, capable of supporting multiple authentication protocols, allowing users to access accounts four-times faster than other two-factor authentication (2FA) and cut support calls by 92%, according to the report. And unlike other 2FA, YubiKeys store no data, require no network connection and don’t run on software — which is why users have experienced zero account takeovers.
The report highlight’s Yubico’s latest all-in-one multi-protocol YubiKey 5 FIPS Series is designed to meet the highest authenticator assurance level (AAL3) requirements from NIST for government and regulated industries.
“YubiKeys provide six, multi-factor authentication protocols all on one physical piece of hardware,” says Frederick, including the ability to support both legacy and modern security protocols, using static passwords, one-time passwords (OTP), PIV (smart card), OpenPGP, FIDO U2F and FIDO2. Additionally, Yubico designed the hardware so that the authentication secret is stored on a separate secure chip built into the YubiKey, so that it cannot be copied or stolen.
“Government agencies can use the YubiKey to bridge the gap to the future,” adds Rob Konosky, director for Yubico’s federal defense business. “There’s no reason to wait to start issuing hardware security keys such as the YubiKey to every single, soldier, sailor, airman and marine that has strong authentication needs.”
Download the full report and learn how Yubico can help accelerate your agency’s journey to zero trust.
This report was produced by FedScoop and underwritten by Yubico.