Rep. Will Hurd blasts IT spending, encryption backdoors
Technology-minded lawmakers are rare on Capitol Hill.
Silicon Valley talent has flooded the executive branch in recent years, but only a handful of tech sector workers have made their way into Congress. Even fewer have a background in computer science. Yet, one of them is now leading the panel that oversees how the government spends its IT dollars.
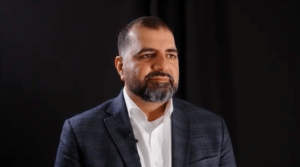
Freshman Rep. Will Hurd, R-Texas, who worked at a small cybersecurity firm called FusionX before he was elected, was appointed chairman of the Information Technology Subcommittee of the House Committee on Oversight and Government Reform this year. He has been quick to weigh in on a number of pressing issues, including the Federal Information Technology Acquisition Reform Act, cybersecurity and encryption.
FedScoop recently sat down with Hurd at his office to discuss the government’s use of IT resources, the FBI’s calls for a backdoor into encryption and the recent cybersecurity bills that have passed the House.
Editor’s Note: This interview has been edited for length and clarity.
FedScoop: In your eyes, is the federal government accomplishing its IT mission? The 2016 budget has $86 billion designated for IT — should that be higher or lower? What do you think the government should be doing better?
Will Hurd: I think the federal government is doing poorly when it comes to leveraging IT resources. Eighty-six billion dollars and 80 percent of that is on legacy systems? That’s outrageous. This is one area where we can be reducing the size and the scope of the federal government.
We have FITARA, which was passed last year — CIOs don’t even have control over the stuff that goes on the network. That’s a problem. FITARA was meant to fix that, and we are going to be doing our oversight to make sure that is happening. This is basic stuff that the private sector does because it’s going to save money. That’s hundreds of millions of dollars right there. The fact that the federal government has over 9,700 data centers, that number should be around 13. We’re not doing a good job because the way we procure IT services is really messed up.
FS: A bill you sponsored that went through markup last week, the DHS IT Duplication Reduction Act, has some language similar to FITARA. How would this work in concert with FITARA?
WH: I think it builds upon FITARA, and in a very specific niche. FITARA is not going to be the end-all, be-all. I think we are going to have to see legislation, especially after the Office of Management and Budget provides its guidance on how to implement it. I think we have a long way to go and we can never do enough to tighten up and eliminate duplication. I think this bill is a companion to FITARA, and you are going to see other small bills that take on a particular element within the various agencies.
FS: Have you talked to Tony Scott since he came on as U.S. CIO?
WH: We have talked. He is a guy who I believe we can work together. We are going to try to sit down and have some more interaction. We are going to figure out how the Oversight and Government Reform Committee, the Government Accountability Office and OMB can work together to solve of these problems.
This is one of those areas where it’s not Republican or Democrat. This about good governance. Not only is that about saving money, it’s about being more efficient and effective in order to do more. We sometimes forget this is about making government better, not just cheaper.
FS: One of DHS’ other focuses is cybersecurity, so let’s address that: A recent Brookings Institution report called the government’s cybersecurity stance “abysmal.” Given breaches at the White House, State Department and OPM, that report’s conclusion has to worry you. What needs to be done to enhance the government’s cybersecurity presence?
WH: The federal government needs to adhere to the same standards that we talk about being important to protecting our infrastructure. We need to empower our CIOs to be the person that is responsible for the implementation of healthy practices on their networks. This is a critical area that’s only going to continue to get more complicated, but you have to have someone who is responsible for that. Right now, the way the existing infrastructure has evolved, we really don’t have that level of accountability.
FS: Is there anything that the government is doing with regard to cybersecurity that could be viewed as a positive?
WH: One of the questions I’ve been asking as I understand the enormity of this task is, ‘Where are people that are doing well?’ and ‘Where can we be mimicking some good things?’ There are some agencies out there that get it. I think within the intelligence services and the military, you have some incredibly capable people, because they are being attacked every single day by the most advanced adversaries that are out there. But we should be comparing ourselves to where we should be, not where we’ve been.
FS: Where do you see strengths in the recent information-sharing bills, like the National Cybersecurity Protection Advancement Act, that have passed through the House?
WH: I’m partial to the elements that I introduced [in that bill], specifically with regards to Einstein 3, moving intrusion detection a little further away from just the junction with the Internet. You’re going to eliminate a lot of known bad traffic from even coming close to our gateways. That’s a very simple technical fix. Also, making sure DHS is focusing on protecting our small and medium-sized businesses. They may not be a direct target of an attack, but to help them not be a drive-by target is important. These are all efforts moving in the right direction, but we can’t get there fast enough.
FS: How much responsibility does the private sector have with regard to cybersecurity and is there anything Washington can do to hold the private sector to a certain standard?
WH: What you are starting to see is the pressure to the bottom lines of these companies and the number of high-profile CEOs that have been fired because of data breaches. That’s going to make a lot of people make sure that they’re following the best practices to protecting digital infrastructure and the information of their customer. I think at the bottom line, profit motive is going to ensure these people are taking the right steps in order to protect their data.
FS: You were recently part of a hearing that looked at law enforcement’s calls for a backdoor into encrypted systems. What was your takeaway from that?
WH: Getting private companies to code in a backdoor is a non-starter. Period. I think the FBI walked away knowing that it’s not even worth bringing that conversation up. We’ve tried this road before, we’ve gone down this road in the ’90s with the Clipper Chip. I appreciate the problem, I get it. But the presumption is that every criminal is Lex Luthor and that’s not the case. Encryption has been around for a very long time. How many examples have there been where a bad guy wasn’t stopped because of encryption? The data is not there. I get this “going dark” phenomenon, but the men and women of law enforcement and the intelligence community are working their tails off to protect us every single day. We have to protect our civil liberties at the same time.
FS: Do you think there is ever going to be a middle ground where law enforcement is happy about encrypted systems?
WH: The better we get at encryption and protecting our digital information, the better it is for everyone. This doesn’t mean that law enforcement is never going to stop a bad guy. It’s going to be how do you adapt techniques and procedures that law enforcement has been using since the dawn of time to stop bad guys.
FS: There has been an influx of talent from Silicon Valley taking top roles in government over the past few months. Can the private sector help the federal government do its job better?
WH: I think so. I think these are people that understand the cutting edge of technology and how to implement it. That’s what we need. That kind of talent is absolutely going to be helpful, but the problem isn’t necessarily at the 30,000-foot view. The problem is how our RFPs [requests for proposals] for IT services are written. This is trench warfare and we’re going to have to get down into the nitty-gritty, into a level of detail, and fix the bowels of the system.
I joked to some IT entrepreneurs at South By Southwest, and I said, ‘I’m in the upper-bottom-third of people that understand technology, but in Washington I’m in the top 1 percent.’ That’s unfortunate, but we are going to do our part to solve some of these problems.