VA investigates breach after federal contractor publishes source code

The Department of Veterans Affairs is conducting a cyber breach investigation after a federal contractor published source code containing sensitive credentials on internet hosting service GitHub, sources told FedScoop.
Three people with direct knowledge of the matter told FedScoop the compromised information included hard-coded administrator account privileges, encrypted key tokens and specific database table information.
After the information was published, six foreign IP addresses cloned the source code, including at least one from a country hostile to the U.S., according to sources.
The cloning of the source code presents a major cyberthreat because it could mean foreign actors have access to application credentials and other data that could assist with lateral movement through an agency’s IT systems.
Sources told FedScoop that as a result of the source code being made public, secret keys used to access at least 12 applications were exposed.
The breach occurred after the contractor allegedly copied source code from a VA-managed GitHub account and published it on their own personal GitHub account, which was then switched to public mode, sources said.
FedScoop was briefed by sources on the condition of anonymity because Congress has not yet been notified about the incident.
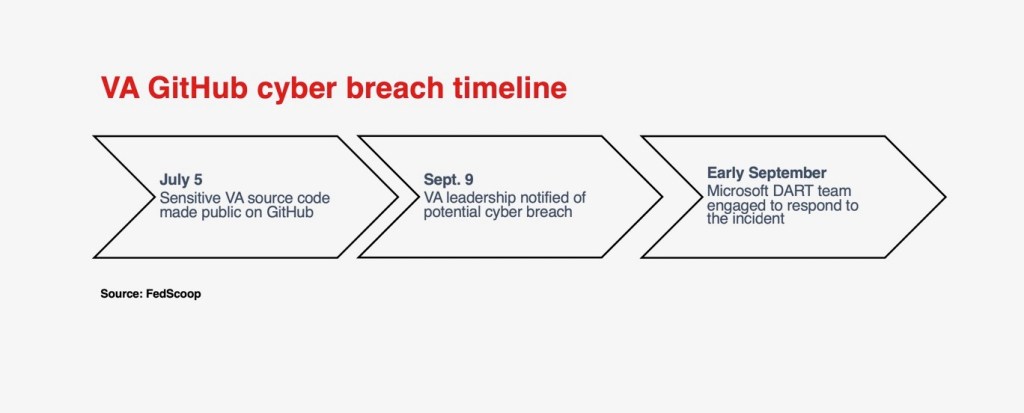
According to sources, publication of the source code occurred on July 5, however IT leadership at the VA was not made aware of the incident until Sept. 9. The breach was discovered through the Cybersecurity and Infrastructure Security Agency’s vulnerability disclosure program and reported to the VA.
Once a government department is notified of a potential breach by CISA, it must then work to verify details of the breach and determine the type and sensitivity of information that may have been compromised.
Microsoft was engaged following the disclosure of incident details to VA IT leadership to provide incident response services. The tech giant provided a detection and response team to conduct an analysis of the security risks posed by the information disclosure, according to three people with direct knowledge of the matter.
GitHub, which is owned by Microsoft, is widely used by government agencies for software development and version control. It is used to provide staff and contractors with a sandbox environment and to facilitate the publication of open-source code.
One source with direct knowledge of the matter said that while the incident does not meet the US-CERT threshold for a major incident, the breach has been designated as a major cyber incident within the VA. This allows the department to engage any internal resources at its disposal, regardless of normal business hours.
However, multiple senior IT officials who spoke with FedScoop said this source disclosure was unusual because, though federal agencies frequently publish open-source code, this involved source code being copied from an official agency GitHub repository and it included sensitive application credentials.
“Copying [source code] from government private side to personal is strictly forbidden, so if the repo was private then that’s a firing and dismissal offense,” said one.
The Federal Information Security Modernization Act requires the Office of Management and Budget to define a major incident, and directs agencies to report major incidents to Congress within seven days of identification.
Under federal law, each government agency is ultimately responsible for determining whether an incident should be categorized as major.
A Department of Veterans Affairs spokesperson said: “First and foremost, no Veteran or VA data has been compromised. On Sept. 9, we were notified that a contract developer copied VA code from an internal source to a personally owned public location. While the software code contained embedded credentials, they were not administrative credentials and did not present a risk to VA or Veteran data.”
They added: “The credentials are part of system-to-system communications that can only be utilized within the VA network. Additionally, VA has no evidence of a data breach or data being cloned by other countries or validated by foreign IP addresses.”
“VA maintains a robust security strategy that includes firewalls, intrusion detection, multifactor authentication, and end-point encryption that reduces the risk of this event causing any harm to veteran or employee data. VA takes the security of Veterans’ and employees’ data seriously and continues to review all code repositories for any additional exposures.”
A CISA spokesperson referred FedScoop to the Department of Veterans Affairs.
Microsoft declined to comment.
Editor’s note: This story was updated to include comment from the Department of Veterans Affairs.






