Fleet Cyber Command creates Operation Cyber Dragon to mitigate vulnerabilities in Navy networks

The Navy has kicked off a repeatable operation aimed at mitigating vulnerabilities on its networks.
Operation Cyber Dragon, which began in March, is focused on identifying and mitigating the attack surface and vulnerabilities of commercial cloud-hosted and externally facing assets over time, Sandy Radesky, Fleet Cyber Command/10th Fleet deputy chief information officer, told FedScoop in a recent interview.
While the Navy does have specialists and services that focus on routine threat mitigation, this effort was distinct in that it focused on more complex commercially provided services.
These systems present more challenges because they sometimes exist in a gray area of either being within the Navy’s portion of the Department of Defense Information Network (DODIN-N) or completely outside that in a commercial space.
“In some of these cases that are a question on is this actually DODIN-N or is this something that’s completely outside of commercial, but related to the Navy in some way, shape or form? The definition of the DODIN is anything leased or owned by the DOD or maybe a DOD component that is responsible. In that aspect, the commercially provided capabilities also fall into that DODIN and category” Radesky said. “There was a bit of ambiguity initially on determining who was accountable and responsible for that terrain and that was a lot of the beginning, first stage of this operation … [The team focused on] accountability roles and responsibility, commercial service provider versus was it actually within the DODIN-N.”
Additionally, Radesky said 10th Fleet wasn’t making as much progress as it would have liked throughout the normal routine efforts it conducts on a daily basis. As a result, a warrant officer developed the strategy to create the operation and bring additional resources to bear.
Specifically, the operation focused on unclassified systems and Impact Level 5 cloud services.
Given how dynamic and changing these environments are, the Navy wanted to conduct a continuous risk understanding and evaluation.
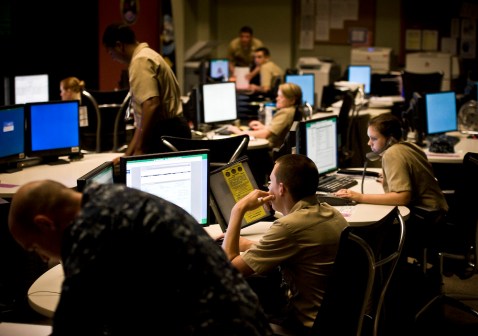
To support Operation Cyber Dragon, the Navy relied heavily on its reserve component.
“We partnered with the U.S. Navy Reserve team that supports Fleet Cyber/10th Fleet to make this be a repeatable operation,” Radesky said. “They come in and help support us and the rest of the Navy CIOs that have commercially hosted capabilities out there that have been identified as vulnerable.”
The operation also used a commercial tool that allowed personnel to view the network externally as if it were an adversary probing it from abroad.
“The views that we look at are external scans looking into what the Navy’s attack surface actually is,” Radesky said. “That is a little bit of a different paradigm than how traditional scanning and vulnerability assessments are done within the known boundaries that you have on your network. This is looking at it from the adversary’s perspective.”
The tool displays to a dashboard that is categorized by geolocation and organization based on the device allowing users to identify a Microsoft Exchange server or an ICS/SCADA system, for example.
“This is what was one of the key benefits of being able to use this on a repeatable basis with a reserve workforce is that it was very intuitive for them to go in there and see this dashboard,” Radesky said. “With that, we have come up with a way to prioritize what we care about from a critical vulnerability standpoint and then bringing that situational awareness dashboard together with the priorities and with the vast terrain that’s organized for us based on our organization, we’re able to rack and stack and put reservists on those tasks on a reoccurring basis for them to work through with the network owners and system owners out there to get after those issues.”
Radesky did not provide specifics regarding the types of vulnerabilities being targeted by the team due to sensitivities but offered they are the types of vulnerabilities in emergency directives released by the Cybersecurity and Infrastructure Security Agency.
So far, the operation has remediated 23% of the 14,000 vulnerabilities initially identified, Radesky said. In the next phase, which kicks off in July, they hope to take care of 50% of the remaining 14,000, though, Radesky noted due to the ebbing and flowing of daily operations, that 14,000 isn’t exact.
Phase II will kick off in mid-July and last about six weeks. It will consist of 75 individuals — which is about three times the number of participants in Phase I — and focus on developing, testing and streamlining standard operating procedures from the first phase by scanning Navy networks, identifying and investigating ownership and continuing to work with Echelon II commands for remediation.