DHS units to re-up contract with controversial mobile device data extractor

The Department of Homeland Security intends to continue its work with Cellebrite, a provider of digital forensics hardware and software tools, according to forecast documents released last week.
Immigration and Customs Enforcement, as well as Homeland Security Investigations, plan to award a five-year, indefinite delivery indefinite quantity contract with a $100 million ceiling to the vendor later this year.
Cellebrite’s products enable the agency to access data from cellphones, tablets and — more recently — unmanned aerial vehicles. The Israeli firm’s data extraction capabilities are “the most widely utilized and deployed computer forensic tool” within HSI, per the document. Cellebrite has been deployed across DHS, including its reported use within the Secret Service to break into the phone of the man who shot President Donald Trump at a campaign rally in Butler, Pa., in 2024.
The vendor provides its data extraction tools to around 7,000 customers across the public and private sectors, including federal agencies outside of DHS. The Department of Justice served as the sponsoring agency for Cellebrite’s pursuit of FedRAMP High Authorization, which it achieved last week after an 18-month process.
Meeting the federal government’s most rigorous cloud security standard eases access across the federal landscape to Cellebrite’s tools and reflects “our commitment to the integrity of the data our technology touches,” said Victor Cooper, senior corporate communications director at the company.
The designation and contract with DHS comes as Cellebrite and the law enforcement agency sharpen focus on drones. DHS created a new office dedicated to easing procurement and deployment of the technology in January. The agency has struck a number of drone-related deals since, and it has spent hundreds of millions of dollars to boost drone-tracking infrastructure and detection technologies across the country ahead of multiple widescale events.
Cellebrite has similarly stepped up its drone savvy. In March, the vendor completed its acquisition of SCG Canada, a leading drone forensics services provider. As part of the deal, Cellebrite will begin offering tools that can unlock more than 80 of the most common UAVs and access their flight logs, video files and cell-tower connections among other data points, according to the company.
“We believe drone forensics will rapidly become one of the most significant data sources for making our nation’s communities and businesses safer,” Cellebrite CEO Tom Hogan said during the company’s Q4 2025 earnings call in February. “Given our leadership in digital forensics and our customers’ trust and dependence on our digital insights, adding drone forensic leadership was both a logical and candidly necessary strategic decision.”
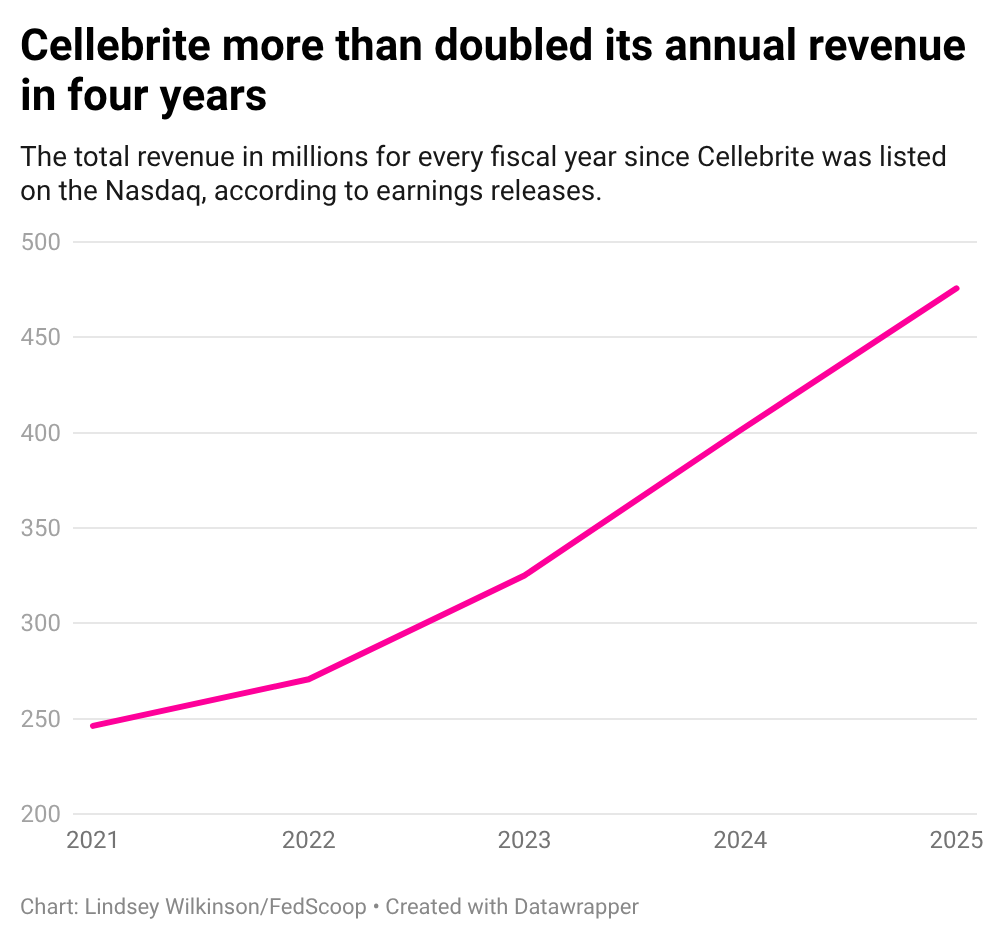
Cellebrite expects its new drone data extraction tools, along with the FedRAMP High Authorization, to drive momentum, per its February earnings call. The company ended fiscal 2025 with revenue growth at around 19% year over year, totalling $475.7 million. It set full-year 2026 expectations for revenue growth between 19% and 20%, with a $571 million ceiling.
Risks, safeguards, concerns
Despite the company’s steady rise toward ubiquity, privacy watchdogs and advocates have qualms about Cellebrite’s tools and how they are being used.
“Cellebrite’s mobile device data extraction tools are extremely invasive,” said Jeramie Scott, senior counsel and director at the Electronic Privacy Information Center’s Surveillance Oversight Program. “These tools can bypass device passcodes and encryption to access the enormous amount of personal information on mobile devices.”
Scott pointed to gaps in oversight and guardrails at ICE and DHS as potential exacerbators of an already risky undertaking.
“The use of data extraction tools needs to be done under the strictest of oversight — something ICE has shown very little interest in,” Scott said via email. “It’s fair to question whether ICE will try to use the border search exception and the broad border zone defined by the government to expand warrantless searches of mobile devices to major cities along the coasts and other areas that fall within the border zone.”
The use of administrative subpoenas, which characterizes a demand issued by a federal agency without prior judicial approval, is a frequent point of contention for privacy advocates.
DHS has used the lever to request data about social media users, garnering pushback from groups like the American Civil Liberties Union. Lawmakers have also called into question the agency’s sprawling data estate and the role that mobile device data is playing.
“I don’t think people realize just how invasive these mobile forensic tools are,” Cooper Quintin, senior staff technologist at the Electronic Frontier Foundation, told FedScoop.
One of Cellebrite’s newer endeavors, dubbed Safeguard Mode, aims to combat device inactivity reboots to give agencies time to get judicial authorization prior to extracting the data. Device inactivity timer features have gained traction among cellphone providers as a way to enhance user privacy and security. After a specified period of the device not being used, the device will reboot and erase stored data. This poses a problem for law enforcement agencies.
Cellebrite, along with other data extraction service providers, are working to sidestep the security enhancement.
“That’s a feature I’m concerned about,” Quintin said. “Depending on how they’re doing it, it requires breaking into the phone. To me, that’s the equivalent of police kicking down your door and standing in the door frame while they wait for the judge to give them a search warrant.”
The company’s tools have been linked to reported human rights violations, and critics have advocated for greater oversight of Cellebrite customers’ usage.
DHS did not respond to a request for comment prior to publication. In response to FedScoop’s questions, Cellebrite emphasized its use of guardrails to prevent misuse and illegal use of its tools.
“At Cellebrite, we believe citizens have a right to keep their personal information free from unnecessary intrusion,” Cellebrite’s Cooper said in an email. “That’s why our tools require valid legal authorization — which includes privacy protections under the law — before any device data is accessed, and our solutions are built exclusively for authorized professionals conducting lawful investigations.”
“Our technology is used in forensic environments after an event has occurred — not to conduct surveillance or monitor individuals,” he added.