DOD’s global flight tracking system needs upgrades, Air Force says
The U.S. Air Force wants to modernize the Department of Defense’s system for global flight information.
The modernization effort for the Defense Aeronautical Information Portal (DAIP) would include creating a “one stop shop” with flight planning, briefing and filing functions, according to the Air Force’s request for information.
On top of creating new software, a contractor would be required to maintain and upgrade existing functions and applications in the portal.
“DAIP provides improved business processes through utilization of modern information technologies and ensures inter-operability between DoD and other Government agencies,” the request stated, but said some of its parts still would still need upgrades by a contractor.
The contractor would be on call 24/7 to support the portal, as its functions guide DOD global flight operations. Information interacts with Federal Aviation Administration flight data and follows its data security requirements.
The DAIP is located in the DISA MilCloud and works both in the internal NIPRNet and internet-based environments.
Personnel is toughest part of starting risk-based cybersecurity programs, agencies say
Most federal agencies lack a cybersecurity risk management program, and leaders say a workforce shortage is the biggest hurdle to developing one.
The Government Accountability Office compared the policies of the 23 civilian Chief Financial Officers Act agencies with risk-based cybersecurity practices and found only seven had a cybersecurity risk management strategy in place.
The departments of Commerce, Labor, and State, as well as the U.S. Agency for International Development, General Services Administration, Office of Personnel Management and Social Security Administration all had strategies assessing the cyber risk of operations, assets, individuals, organizations, and the nation. Sixteen other agencies did not.
“Without ensuring that their policies include all key risk management activities, the agencies may not be taking the foundational steps needed to effectively identify and prioritize activities to mitigate cybersecurity risks that could result in the loss of sensitive data or compromise of agency systems,” reads the GAO report.
All 23 agencies cited challenges hiring and retaining key cyber management personnel as the biggest barrier to establishing a program, followed by operational conflicts, and then inconsistent policies and procedures.
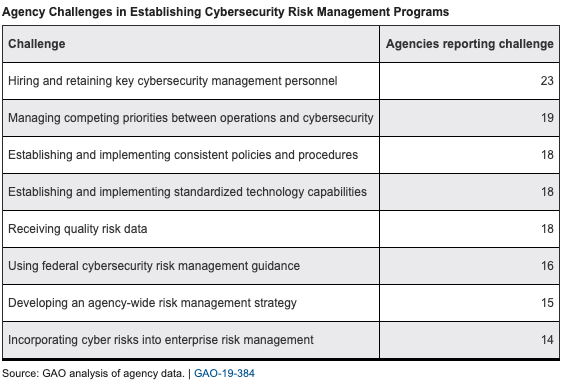
When it came to appointing a cyber risk executive, all but one agency, GSA, reported having a chief information officer, chief information security officer or other entity providing agency-wide oversight. GSA said that role was shared by multiple officials, but GAO was not convinced.
“[W]ithout clearly defining and documenting the responsibility for the risk executive function, the agency may lack consistent implementation and oversight of cybersecurity risk management activities and an effective agency-wide view for managing risk,” reads the report.
Additionally 17 agencies were found to lack policies for assessing cyber risks using scorecards or dashboards, with some reporting they still needed to acquire tools for aggregating system-level data.
And 13 agencies failed to coordinate between cyber and enterprise-wide risk management (ERM) programs via a council or reporting briefings. Some even lacked an ERM governance structure altogether, according to the report.
GAO recommended agencies remedy those deficiencies and directed the Office of Management and Budget and the Department of Homeland Security to provide additional guidance and assistance mitigating barriers.
President Trump’s May 2017 executive order on strengthening cybersecurity called for initiatives addressing some of the challenges to risk management: hiring and retention, standardizing capabilities, receiving quality risk data, and using guidance.
A total of 17 agencies agreed with GAO’s recommendations, three took no position, and two along with OMB did not comment. The Department of Health and Human Services argued its information security and privacy policy already addresses security and privacy controls.
“However, while these policy statements require adherence to [National Institute of Standards and Technology] and OMB standards for selecting security controls and require a rationale for tailoring decisions, they do not specifically require the use of risk assessments to inform the tailoring of security controls,” reads GAO’s report.
GAO reminds agencies of FISMA requirements, says OMB report is overdue
The typical federal agency still has familiar deficiencies in its information security practices, according to a Government Accountability Office survey of implementation of one of the government’s key cybersecurity laws.
As of fiscal 2018, “many federal agencies were often not adequately or effectively implementing their information security policies and practices” under the Federal Information Security Modernization Act of 2014, or FISMA, the report says.
The GAO also says the White House Office of Management and Budget (OMB) is behind on one governmentwide requirement — a report to Congress on FISMA compliance for fiscal 2019.
The report is the latest update from GAO on cybersecurity issues covered in its famous High Risk List. Individual agencies have drawn their own dedicated reports in recent months, including the Census Bureau and the Internal Revenue Service. Governmentwide, the GAO recently examined how agencies are handling legacy IT systems.
The latest study looked at 16 “randomly selected” agencies, including 12 covered by the management rules of the 1990 CFO Act and four smaller ones. Most were meeting FISMA’s goals for security training, incident response and taking remedial actions. The group was less successful in implementing periodic risk assessments; periodic testing and evaluation of controls; and preparations for continuity of operations. Only four of the 16 complied with FISMA’s call for “subordinate plans for providing security” — for example, plans for individual networks or facilities.
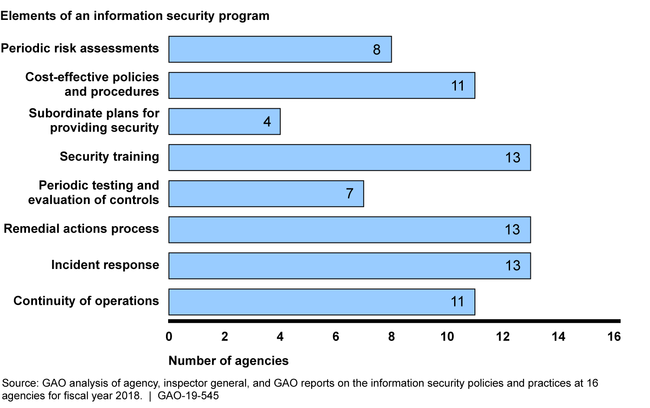
The GAO also called out the 24 CFO Act agencies, in general, for failing to meet FISMA’s requirement for agencywide information security programs. Only six had them.
The bright spot in the report comes from the agencies responsible for helping direct federal cybersecurity. OMB, the Department of Homeland Security (DHS) and the National Institute of Standards and Technology (NIST) are “generally implementing” their requirements under FISMA, the report says, “including issuing guidance and implementing programs that are intended to improve agencies’ information security.”
The survey of 16 agencies examined FISMA compliance at the departments of Agriculture, Commerce, Education, Housing and Urban Development, Justice, Labor, State, and the Treasury, as well as the EPA; Federal Communications Commission; Federal Retirement Thrift Investment Board; Merit Systems Protection Board; NASA; Presidio Trust; Small Business Administration; and the Social Security Administration.
DOD must clear up some cybersecurity rules for contractors, IG audit says
Defense contractors remain a weak link in the Department of Defense’s cybersecurity, but current regulations are hampering potential improvements, according to a new DOD inspector general report on the handling of controlled but unclassified information.
The report notes basic cybersecurity practices — such as multi-factor authentication, strong passwords and reviewing system activity reports — where not being followed by the nine randomly selected contractors the IG investigated.
Top Defense officials told investigators, however, that they couldn’t mandate strong passwords and automatic logouts for contractors, citing conflicts with existing federal regulations as well as Executive Order 13556 from 2010. The regulations set the scope for management of controlled but unclassified information.
One of the two rules, 32 Code of Federal Regulation section 2002, states in part agencies “may not implement safeguarding or dissemination controls for any unclassified information other than those controls consistent with the [controlled unclassified] Program.” The IG disagreed that the regulation blocks the DOD from implementing cybersecurity practices such as using strong passwords.
DOD officials concurred, though, with the need for broad reviews of how information is handled by contractors and the DOD.
The report also cites some communication failures. A failure to properly mark controlled but unclassified information, for example, blinded contractors to what steps they needed to take to ensure information security. DOD contracting offices “inconsistently tracked” which contractors had what type of information, leaving both sides of the contracting process in the dark, the report states.
The DOD is in the process of revamping the cybersecurity standards, which are based on documents from the National Institute of Standards and Technology. Contractors have struggled to follow them, so the Pentagon developed its own model called the Cybersecurity Maturity Model Certification. The new standards are projected to be a required part of DOD contracting early next year, according to Pentagon officials.
While the report set out to investigate the handling of unclassified information, it noted that a DOD contracting office did not take appropriate action to address a spillage of classified information to unclassified environments.
“Neither the Defense Threat Reduction Agency nor the contractor took prompt action to report and address the spillage of classified DoD information,” the report stated.
Official responses from contracting and cybersecurity officials agreed to “implement a plan to verify” that cybersecurity weaknesses are corrected. The DOD IG requested further comments from many of the officials quoted in the report on steps they plan to take to improve information security. While 20 of the 45 recommendations from the IG have been implemented in DOD agencies, only four have been verified, according to the report.
If it’s new tech, be sure to test it, GAO tells Census Bureau
Federal officials and lawmakers pressed the Census Bureau to increase testing of new technologies being used in the 2020 census, lest they jeopardize the integrity of the population count.
The bureau estimates the census will cost $15.6 billion, a $3 billion increase over its original estimate. To save money the bureau plans to increase automated data collection, use administrative records when it can, verify addresses with aerial imagery, and allow internet responses for the first time.
New technologies introduce new risks to the census count “in part because they have not been tested extensively, if at all,” said Robert Goldenkoff, director of strategic issues at the Government Accountability Office, during testimony before the House civil rights subcommittee on Wednesday. In 2017 and 2018, the bureau scaled back operational tests, citing budget uncertainties.
“Without sufficient testing across the range of geographic locations, housing types, living arrangements, and demographic groups, operational problems can go undiscovered,” Goldenkoff said. “And the opportunity to refine procedures and systems could be lost.”
While the bureau has made “important progress” in mitigating some risk, Goldenkoff said, it’s been on GAO’s High Risk List since February 2017 and is delayed in addressing 104 corrective actions in areas like operations, information technology and cybersecurity.
Bureau Director Steven Dillingham said the bureau rigorously scans for vulnerabilities each month, addressing about 100 risks a month from a running list of 300.
“There will be risk identified and risk coming off, so we’re working the list,” Dillingham said. “And that’s actually the way GAO recommends we do business.”
“I would never envision that risk list reaches zero,” he added.
A June Department of Commerce Office of Inspector General report found severe risks to census cloud environments, where respondents’ personally identifiable information will be stored.
“The bureau is home to one of the largest databases of identifiable, personal information on the American people,” said Rep. Jamie Raskin, D-Md., chairman of the subcommittee. “The security of this data is paramount, not only to a well-run census, but to the public’s confidence in our system.”
Dillingham said the environments hadn’t been breached, but the bureau needed to ensure no one had special access to them and they could be taken down in a way that left no data behind.
“Immediate action was taken; it was some time ago,” he said. “It involved contractors and setting up the system.”
Most of the corrective actions have been made, he added, with the remainder monitored weekly.
A total of 52 IT and cybersecurity systems will be used at different census stages, the bureau recently delivering two new ones for early hiring and training. The next few months will see testing and production deadlines for many additional systems — five of which the bureau is at risk of missing, according to GAO.
Deliveries supporting internet self response and recruiting and hiring for peak operations need to be “closely monitored” because they are fast approaching, said Nicholas Marinos, director of IT and cybersecurity at GAO.
While most of the 52 systems received initial authorities to operate (ATOs), five are still awaiting authorization, and nine require their security controls be reassessed prior to the census due to additional development work.
The census begins in Alaska in less than six months and the nationwide count in March. The resulting population data is used in redistricting and apportioning billions of dollars reaching millions of people through federal, state and local programs and services.
When it comes to data collection, the bureau is using the “latest, state-of-the-art softwares (sic)” and encryption while working with agency partners and “major, high-tech companies,” Dillingham said.
“We can no longer rely on collecting data in the usual ways and places,” Dillingham said. “With internet and phone options, we have the tools to go into the less-visible, hard-to-count areas and collect the data.”
Suzette Kent: Toughest challenges in federal AI adoption will be in ‘middle’ layer
Federal agencies have seen some early success adopting artificial intelligence but still face major challenges as they look to apply the technology to business processes and service delivery — things that require explainability — U.S. CIO Suzette Kent said Thursday.
“The journey now is to the much more difficult things,” she said.
So far, most agencies have focused on automating simple manual workloads, taking baby steps in exploring AI. Others have used the technology to “leapfrog” into addressing some “exciting” more but complicated applications, Kent said at a Partnership for Public Service event. “There is not a single agency that’s not doing something.”
It’s in the middle between those two ends of the adoption spectrum, however, that the federal government is “making a little bit slower progress” and will face the biggest challenges that AI will present in the public sector.
The middle is “where we have to cross many silos,” Kent said. “It’s easy to automate a manual task. But when you significantly change a business process, you have to look at the human resources, you have to look at how we engage with customers, you have to look at how we collect data and what the regulatory environment looks like for how we’re collecting it and what we’re using or how we’re using it. We have to retrain a broader swath of employees. The work in the middle that really changes the business process and the service delivery is the tougher work.”
On top of that, there’s the difficulty in providing transparency and explainability when AI provides a solution. With a human at the other end, an agency must be able to show how it got to a decision using artificial intelligence, Kent said.
“As the use cases move from the manual tasks to that middle and the higher end — where we are closer to delivery of services to citizens and decisions about things that we do have more human impact — we have to have a mechanism for explaining and being transparent that is very different than what we have today,” she said.
Using AI to monitor for and identify fraud, for example, is “pretty explainable” Kent said. “We know how that was supposed to go. But when we have to explain the construct of a complex decision with many different data sets, that changes the paradigm.”
Levels of communication
The need for explanation will require better communication skills among the technical teams working with AI in the federal government.
“How we might explain something to a group of scientists and what’s explainable in that population is very different from how we might explain why someone was chosen to receive a food supplement benefit,” Kent said. “That is a set of skills … beyond the technical, beyond the data disciplines, the next step in how we interact with citizens we’re serving.”
The Office of Management and Budget is working through this challenge and developing policy to “serve as guideposts for AI,” Kent said. That includes “controls and expected examination of responsibilities, both of data and what’s in the algorithms, so that we’re starting with safety and we’re starting with careful thought.”
Nevertheless, agencies are doing a “phenomenal job” with the “easy stuff” of AI, she said, urging them to continue on that path while exploring how to move on to addressing this next, thornier middle piece. Those teams using AI are also “much happier because the work they’re doing is a lot more interesting.”
“It’s driving more valuable work. And it’s actually showing us where we need to make more investments in skills,” Kent said. “In almost every agency, what you’ll hear them say is, ‘Yes we are starting with the manual, repetitive tasks.’ But those same individuals are now doing more value-added work.”
The Partnership for Public Service released a report Thursday on building trust and managing risk around the adoption and use of AI.
Rubio, House Republicans write more letters requesting JEDI delay
Republicans on Capitol Hill continue to press for a delay in the Pentagon’s $10 billion Joint Enterprise Defense Infrastructure (JEDI) contract following President Trump’s remarks that the White House would “take a very strong look at” the acquisition.
GOP lawmakers sent two letters this week. A dozen House Republicans wrote to Trump on Tuesday urging him to halt the contract. Sen. Marco Rubio, R-Fla., sent his second letter in recent weeks Thursday asking Defense Secretary Mark Esper to wait on the highly contentious contract.
Earlier this month, the JEDI contract cleared a major hurdle after the Pentagon prevailed in a months-long slog in the Court of Federal Claims prompted by Oracle, whose lawsuit claimed the acquisition limited competition and that former department officials were in a conflict of interest with Amazon Web Services. That clears the path for DOD to move forward awarding the contract sometime in August for enterprise commercial cloud capabilities that would, theoretically, extend to the battlefield. Just Microsoft and AWS remain in competition for the contract. Oracle and IBM did not survive earlier portions of the acquisition process.
Both Rubio and the House Republicans asked that the contract be delayed to await an ongoing inspector general report regarding DOD employees who worked on the JEDI deal and reportedly did not properly disclose work for unnamed private companies. The letters are likely referring to the contract’s leading contender, Amazon Web Services.
The DOD contracting officer leading the JEDI acquisition earlier cleared the contract to move forward, saying there had been “no adverse impact on the integrity of the acquisition process.” However, the official’s “investigation also uncovered potential ethical violations, which have been further referred to DOD [inspector general],” according to a Pentagon spokeswoman.
“These admissions are highly concerning in a major procurement, which should proceed free of any bias or conflict,” Rubio’s letter stated, referring to the alleged conflicts of interest.
The federal claims court has also already ruled that “organizational conflict of interest does not exist and that individual conflicts of interest did not impact the procurement.”
Rubio doesn’t sit on any defense-related committees and tends to focus on foreign policy issues, but he occasionally will weigh in on technology topics. During the 2016 election cycle, Oracle Executive Chairman Larry Ellison donated $5 million to the pro-Rubio super PAC Conservative Solutions and gave $350,000 to another pro-Rubio PAC, the Florida First Project, according to Open Secrets. Rubio’s office declined to comment.
Other lawmakers, meanwhile, want the Trump administration to get moving on the JEDI contract. Following the president’s remarks about it, a group of four Republican House members wrote a letter urging the president to consider the national security implications of the contract.
“My view is that moving to the cloud is essential — we are behind in doing so,” Rep. Mac Thornberry, R-Texas, told FedScoop during a reporter roundtable Wednesday.
GSA begins transition to new identifier replacing DUNS
July marks the start of the 18-month shift to a new unique entity identifier (UEI) for doing business with the government.
In December 2020, the System for Award Management website, SAM.gov, will stop using the proprietary, nine-digit Data Universal Numbering System (DUNS) number supplied by Dun & Bradstreet.
The General Services Administration selected Ernst & Young to supply a non-proprietary UEI for identifying entities during the awards process for things like contracts, grants and cooperative agreements — in SAM.gov and other systems.
While GSA develops tools to generate new UEIs and begins assigning them, the DUNS number will remain the official UEI for registering with SAM.
GSA is also streamlining UEI request, registration and support processes by allowing entities to handle all three through SAM.gov. Previously Dun & Bradstreet assigned DUNS numbers before entities could register on SAM.gov and provided technical support.
In the future, SAM.gov will assign UEIs as 12-character alpha-numeric values — all letters being capitalized.
UEIs won’t use the letters O or I to avoid confusion, use 0 as the first character for ease of data imports, use nine-digit sequences like the DUNS number, have the first five characters conflict with Commercial and Government Entity codes, be case sensitive, or contain the entity’s Electronic Funds Transfer indicator. The final character will be a checksum of the first 11 to detect errors in data.
The entities required to register on SAM.gov haven’t changed, and all forms using the DUNS number will be updated.
UEIs will automatically be assigned to existing entities within SAM.gov and made available for viewing. Large businesses with multiple DUNS numbers will receive multiple, corresponding UEIs.
During the transition phase, entities assigned UEIs will still need to ensure that the agency they’re responding to has switched over to the new identifier or else continue using their old DUNS number.
GSA has provided and explainer video with more details.
GAO: VA isn’t properly tracking maintenance costs of VistA
The cost just to maintain the Department of Veterans Affairs’ legacy electronic health record VistA over the last three years was $2.3 billion. Maybe. The VA doesn’t really know.
The VA doesn’t have an accurate price tag for the decades-old system — formally known as the Veterans Health Information Systems and Technology Architecture — because it doesn’t know where the functions of VistA begin and end, Carol Harris, director of information technology acquisition management at the Government Accountability Office, said Thursday in an oversight hearing.
Harris referenced a GAO report she authored on VistA released Thursday detailing the lack of effective cost-tracking for fiscal 2015-2017. The report stated the VA didn’t follow “well-documented methodology” on cost tracking.
“Doing so is essential,” Harris added of the need for better accounting.
Cost-tracking is made particularly important by the VA’s multibillion-dollar transition to a modernized EHR developed by Cerner. The contract states the VA needs to provide Cerner with detailed information on VistA for a successful transition. But without a detailed understanding of the VistA system and accurate tracking of costs, that migration is at risk, according to the GAO report.
It’s a problem 30 years in the making. VA officials responsible for VistA told the GAO that they have not been able to fully define the system because its creation was decentralized, leaving few at the department decades later with authoritative knowledge of the full scope of the portfolio.
“Money doesn’t grow on trees,” Rep. Susie Lee, D-Nev., chair of the House Committee on Veterans’ Affairs Tech Modernization Subcommittee, told officials from the VA.
VA’s new EHR program, a $16 billion endeavor dubbed the Electronic Health Record Modernization, is already showing some initial successes and savings, Paul Tibbits, director of the Office of Technical Integration at the VA, said in testimony
The hope is the system will be “similar” to the Pentagon’s to have “seamless” transitions when service members separate from the military and fall under VA care, then-Secretary David Shulkin said in 2017.
The new system will absorb only 60 percent of the VistA portfolio, said John Short, the chief technology integration officer for the agency’s EHR office. The other 40 percent of services will be taken over by other modernization efforts, such as financial management and other mostly non-health related duties.
AI needs more public-private partnerships, says OSTP’s Droegemeier
Spending on non-defense and non-classified artificial intelligence research and development has hovered at around $1 billion, but the White House’s Office of Science and Technology Policy wants more to be done to support public-private partnerships, Director Kelvin Droegemeier said Wednesday
But beyond just funding levels, there is still more work to be done to lead in the burgeoning AI industry, Droegemeier said
“We kind of have a V-8 engine running on six cylinders,” he said in an energetic testimony before the House Subcommittee on Commerce, Justice, Science, and Related Agencies.
OSTP has been the hub for coordinating guidance and regulations non-defense AI and machine learning work since the Obama administration published the National Artificial Intelligence Research and Development Strategic Plan in late 2016. This June, the Trump administration updated the plan to include a call for more public-private partnerships.
President Trump signed an executive order to spur AI research in February. The strategy was the administration’s cohesive plan for boosting AI support and laid out a “multi-pronged approach” to leading in the field. Now, Droegemeier wants to get more groups, from academia to private industry, at the AI table.
“In America, we don’t do nearly as well with partnerships as we really could,” he said.
Beyond just government research, Droegemeier wants to see more use of AI and machine learning to help the government serve citizens. For instance, to help veterans separating from service, advanced data analytics can be used to put them on pathways using skills beyond what they did in the military, he said.
Droegemeier also faced questions on how to improve research environments and diversity in the science, technology, engineering and math (STEM) field.
“The research environment has got to be right,” Droegemeier said. “I dream of the days we can make [safe spaces] happen.”
Focusing on increasing the diversity of the types of workers in STEM field is a priority of the Trump administration, Droegemeier said, pointing at Ivanka Trump’s “Pledge to America’s Worker” program and upskilling and reskilling programs.